|
#2
7th August 2014, 10:35 AM
| |||
| |||
| Re: UGC NET JRF Computer Science Paper II Solved Paper
Here I am giving you solved question paper for University grant commission NET JRF Computer Science Paper II. 2. The worst case time complexity of AVL tree is better in comparison to binary search tree for (A) Search and Insert Operations (B) Search and Delete Operations (C) Insert and Delete Operations (D) Search, Insert and Delete Operations 3. The GSM network is divided into the following three major systems : (A) SS, BSS, OSS (B) BSS, BSC, MSC (C) CELL, BSC, OSS (D) SS, CELL, MSC 4. The power set of the set {} is (A) {} (B) {, {}} (C) {0} (D) {0, , {}} 5. If the disk head is located initially at 32, find the number of disk moves required with FCFS if the disk queue of I/O blocks requests are 98, 37, 14, 124, 65, 67. (A) 239 (B) 310 (C) 321 (D) 325 6. Component level design is concerned with (A) Flow oriented analysis (B) Class based analysis (C) Both of the above (D) None of the above 7. The ‘C’ language is (A) Context free language (B) Context sensitive language (C) Regular language (D) None of the above 8. The Mobile Application Protocol (MAP) typically runs on top of which protocol ? (A) SNMP (Simple Network Management Protocol) (B) SMTP (Simple Mail Transfer Protocol) (C) SS7 (Signalling System 7) (D) HTTP (Hyper Text Transfer Protocol) 9. If a packet arrive with an M-bit value is ‘l’ and a fragmentation offset value ‘0’, then it is ______ fragment. (A) First (B) Middle (C) Last (D) All of the above 10. The number of bit strings of length eight that will either start with a 1 bit or end with two bits 00 shall be (A) 32 (B) 64 (C) 128 (D) 160 11. In compiler design ‘reducing the strength’ refers to (A) reducing the range of values of input variables. (B) code optimization using cheaper machine instructions. (C) reducing efficiency of program. (D) None of the above 12. In which addressing mode, the effective address of the operand is generated by adding a constant value to the contents of register ? (A) Absolute (B) Indirect (C) Immediate (D) Index 13. Which of the following is true ? (A) A relation in BCNF is always in 3NF. (B) A relation in 3NF is always in BCNF. (C) BCNF and 3NF are same. (D) A relation in BCNF is not in 3NF. 14. Given memory partitions of 100 K, 500 K, 200 K, 300 K and 600 K (in order) and processes of 212 K, 417 K, 112 K, and 426 K (in order), using the first-fit algorithm, in which partition would the process requiring 426 K be placed ? (A) 500 K (B) 200 K (C) 300 K (D) 600 K 15. What is the size of the Unicode character in Windows Operating System ? (A) 8-Bits (B) 16-Bits (C) 32-Bits (D) 64-Bits 16. In which tree, for every node the height of its left subtree and right subtree differ almost by one ? (A) Binary search tree (B) AVL tree (C) Threaded Binary Tree (D) Complete Binary Tree 17. The design issue of Datalink Layer in OSI Reference Model is (A) Framing (B) Representation of bits (C) Synchronization of bits (D) Connection control 18. Given the following expressions of a grammar E E * F / F + E / F F F – F / id Which of the following is true ? (A) * has higher precedence than + (B) – has higher precedence than * (C) + and – have same precedence (D) + has higher precedence than * UGC NET Computer Science Paper II Solved Paper 2. In order that a code is error correcting, the minimum Hamming distance should be : (A) t (B) 2t - 1 (C) 2t (D) 2t + 1 Ans:-D Explanation:- The error-detecting and error-correcting properties of a block ode depend on its hamming distance. To reliably DETECT ’t’ errors, you need a distance t+1 code. To CORRECT t errors, you need a distance 2t+1 code. 9. With four programs in memory and with 80% average I/O wait, the CPU utilisation is? (A) 60% (B) 70% (C) 90% (D) 100% Ans:-A Explanation:-CPU utilisation is given by the formula = 1 - P pow n CPU utilisation is calculated from a probabilistic viewpoint. P stands for the fraction of time waiting for I/O to complete. Number of processes in memory = n The probability that all n processes are waiting for I/O is p pow n. P=80%=80/100=0.8 n=4 CPU Utilization = 1 - p pow n = 1 - (0.8) pow 4 = 1 - 0.4096 = 60% 28.A binary tree is said to have heap property if the elements along any path: (A) from leaf to root are non-increasing (B) from leaf to root are non-decreasing (C) from root to leaf are non-decreasing (D) from root to leaf are non-increasing Ans:- D Explanation:-Answer is in Schaum’s series book on Data structures with C++. A binary tree is said to have the heap property if the elements along any path from root to leaf are non increasing. A heap is a complete binary tree that has the heap property. So the correct option is D. 33. In which addressing mode the operand is given explicitly in the instruction itself? (A) Absolute mode (B) Immediate mode (C) Indirect mode (D) Index mode Ans:- B Explanation:- In immediate addressing mode, the operand is given in the instruction itself. Eg:- MOV AL,64H Move 64H to Al register MOV Bx,0493H Move 0493H to Bx register. 42. Which of the following is used for test data generation? (A) White box (B) Black box (C) Boundary-value analysis (D) All of the above Ans:-C Explanation:- Boundary value analysis is a technique for test data selection.A test engineer chooses values that lie along data extremes UGC NET Computer Science Paper II Paper    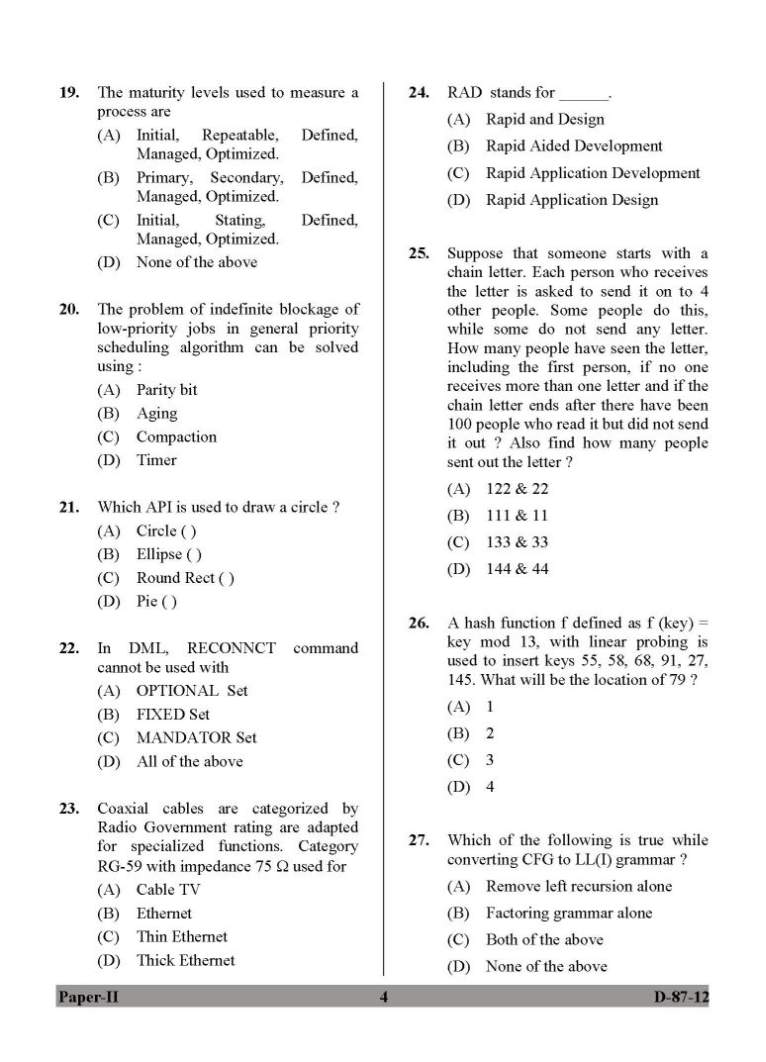 in a file attached with it so you can get it easily |